I'm a retired software engineer so I focus here on the technological risks. I have no positions in cryptocurrencies or related companies. Nearly a quarter-century ago I started work at Stanford on a decentralized peer-to-peer consensus system using Proof-of-Work. It won a Best Paper award five years before Satoshi Namakoto published the Bitcoin protocol.
This discussion is badly framed; the term "digital asset" is counter-productive. My checking accounts are digital assets. What you want to talk about are "cryptocurrencies" or "digital ledger technologies" or "blockchains", but these terms cover two completely different technologies:
- permissioned or centralized systems with an obvious locus of control to which regulations can be applied,
- and permissionless or decentralized systems which claim to lack a locus of control, and thereby to be immune from regulation.
That a system is permissionless is a fact, that it is decentralized is a claim. In practice the claim is false, they do have loci of control. The spurious claim is used to deter regulation, so don't accept it by using the "decentralized" word.
 |
| Source |
Centralized systems, whether they use a conventional database or a permissioned blockchain, don't raise significant new risks or regulatory problems, but permissionless systems do. They are not fit for purpose in at least five areas:
- Consensus
- Anonymity
- Immutability
- Privacy
- User Experience
 |
| Source |
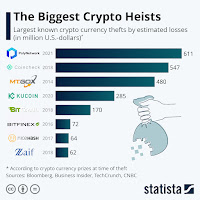
 |
| Source |
Second, users of permissionless systems can create arbitrarily many identities, pseudonyms. Newly created pseudonyms are anonymous, but in systems such as Bitcoin and Ethereum as they become enmeshed in the web of transactions they can be linked to real-world identities fairly easily.
 |
| BitFinex loot transfers |
More sophisticated miscreants use "mixers" such as Tornado Cash, or coins such as Monero or Zcash that use advanced cryptography to obscure transactions. These capabilities of permissionless cryptocurrencies enable a massive crime wave including sanctions evasion, ransomware and drug dealing. Further, even with escrow "smart contracts", users cannot safely purchase physical goods.
 |
| Source |
Fourth, the history of transactions in a permissionless system is necessarily public. Maintaining anonymity requires operational security beyond ordinary users' ability. Thus in practice most users' transaction history is effectively both public and immutable, enabling abuse and harassment on an unprecedented scale.
Fifth, because of the catastrophic nature of mistakes, users of these purportedly "trustless" systems generally do not access permissionless systems directly, but must place their trust in a user experience layer above the base system's API. As is normal in software, increasing returns and network effects mean that these layers have one or two dominant applications (Alchemy and Infura for Ethereum, for example). A compromise of these systems would place the whole ecosystem at risk.
 As you see, permissionless cryptocurrency technology really doesn't work well at all. Evidence for this is the need for so-called "layer-2 systems" such as the Lightning Network, which doesn't really work either. So why put up with this inadequate technology? To deflect regulation so that the insiders and the criminals can continue to rip off everyone else. Encouraging "responsible development" of a technology whose main purpose is to enable irresponsibility is a fool's errand.
As you see, permissionless cryptocurrency technology really doesn't work well at all. Evidence for this is the need for so-called "layer-2 systems" such as the Lightning Network, which doesn't really work either. So why put up with this inadequate technology? To deflect regulation so that the insiders and the criminals can continue to rip off everyone else. Encouraging "responsible development" of a technology whose main purpose is to enable irresponsibility is a fool's errand.
8 comments:
Gilead Edelman's Crypto and the US government are headed for a decisive showdown is a good overview, concluding:
"If you think cryptocurrencies are a stupendous innovation that will unlock all kinds of hitherto impossible use cases, then you might think it’s crucial to craft a supple regulatory regime that helps the sector thrive at the expense of elaborate investor protections. If, on the other hand, you remain unconvinced that crypto has done anything but fuel a speculative asset bubble, you probably don’t think that. You might conclude, instead, that an industry that can’t exist if it must obey laws meant to protect investors is not an industry worth saving."
People in the first ggroup are Talking Their Book.
Bob Van Voris reports in IRS Seeks SFOX Customer Information in Cryptocurrency Tax Push that:
"The Internal Revenue Service is seeking to identify customers of cryptocurrency prime dealer SFOX Inc. as part of its efforts to force crypto investors to pay taxes on their holdings.
In court filings in New York and Los Angeles, the tax authority asked federal judges to let it serve summonses on SFOX and M.Y. Safra Bank, which partnered with SFOX in 2019 to offer its customers cash deposit accounts backed by the Federal Deposit Insurance Corporation. The IRS is seeking account and transaction records for users with cryptocurrency transactions over $20,000 in any year from 2016 to 2021."
And Leah Nylen reports in FTC Probes BitMart Exchange Breach, Marking Agency’s First Crypto Case that:
"The Federal Trade Commission is investigating the operators of the BitMart cryptocurrency exchange over a December 2021 hack that led to consumer losses between $150 million and $200 million -- marking the agency’s first known probe into crypto markets.
The investigation was disclosed Wednesday in an FTC order denying a bid by BitMart operators Bachi.Tech Corporation and Spread Technologies LLC to block the agency’s efforts to compel them to turn over information. The companies had argued that the FTC’s document request was overly broad and that some of the information was located overseas."
Michael del Castillo reports that Every U.S. Crypto Exchange (And Binance) Is Being Investigated By The SEC, Says Senator Lummis Staffer:
"Widely circulated reports that the U.S. Securities and Exchange Commission (SEC) is investigating $20 billion crypto exchange Coinbase are just the tip of the iceberg, according to a staffer from U.S. Senator Cynthia Lummis’ (R-Wy) office. The staffer says every U.S. crypto exchange—and the largest crypto exchange in the world, Binance—are in various stages of being investigated. There are more than 40 U.S. cryptocurrency exchanges, according to crypto data site, CoinGecko."
This is obviously why Sen. Lummis is so focused on making the CFTC the cryptocurrency regulator.
SEC chair Gary Gensler's WSJ op-ed is entitled THE SEC TREATS CRYPTO LIKE THE REST OF THE CAPITAL MARKETS:
"We can dispense with the idea that crypto lending isn’t subject to regulation. On the contrary, the rules have been around for decades. The platforms aren’t following them. Non-compliance is not the inevitable result of the crypto business model or underlying crypto technology. Rather, it is as if these platforms are saying they have a choice—or even worse, saying “Catch us if you can.”
As I said in a speech last year, “Make no mistake: If a lending platform is offering securities, it . . . falls into SEC jurisdiction.” On many occasions, the commission and state regulators have addressed how the relevant case law implicates crypto assets, including crypto lending.
There are costs of complying with securities laws, just as there are costs to car makers of adding seat belts. Platforms that offer crypto lending need to comply anyway, not merely because that’s the law, but also because it helps protect investors and increase trust in our markets."
Back in May Nicholas Weaver posted OFAC, the DPRK and the Tornado of Cash suggesting that:
"OFAC should consider a creative sanction against Tornado Cash, particularly the 100 Ethereum wallet. This wallet itself should be listed as a sanctioned entity because it is known to be hiding a large amount of the DPRK’s stolen cryptocurrency."
Earlier this month OFAC followed Weaver's suggestion. Now, Weaver follows up with OFAC Around and Find Out:
"On Aug. 8, OFAC announced the addition of virtual currency mixer “Tornado Cash” and all of its wallets to the Specially Designated Nationals and Blocked Persons List (SDN list), of entities that it is illegal for U.S. persons, or really anything that touches the U.S. financial system, to do business with.
...
the organization responsible for Tornado Cash, the Tornado Cash “DAO” (decentralized autonomous organization, basically a corporation that doesn’t bother to do the paperwork to gain the legal protections of a corporation), decided to fold up shop as they “can’t fight the U.S.” government, freezing future development and transferring funds initially intended to support continued development of the system to those who invested in the Tornado Cash governance token."
Back in June last year Weaver posted How to Start Disrupting Cryptocurrencies: “Mining” Is Money Transmission:
"Miners then choose from the set of valid [transactions] they want to include and collect them together in a “block.” ... During this process the miners are making active decisions on which [transactions] to include."
Weaver now writes:
"OFAC should offer a “friendly” reminder to all U.S.- and U.S.-adjacent-based cryptocurrency miners that they have an obligation to follow OFAC regulations. OFAC should elaborate that a miner that produces a block is responsible for the transactions contained in the block."
But Ethereuem mining is heavily concentrated - right now three mining pools control 53.2% of the mining power. And it is the pools, not the individual miners, which determine the contents of a block. Thus the "friendly" reminder should go to the pools as well as the miners.
Kurt Opsahl of the EFF posted Code, Speech, and the Tornado Cash Mixer:
"The issues EFF is most concerned about arise from speech protections for software code and how they relate to government attempts to stop illegal activity using this code. This post outlines why we are concerned about the publication of this code in light of what OFAC has done, and what we are planning to do about it."
The key concern is:
"EFF’s most central concern about OFAC’s actions arose because, after the SDN listing of “Tornado Cash,” GitHub took down the canonical repository of the Tornado Cash source code, along with the accounts of the primary developers, including all their code contributions. While GitHub has its own right to decide what goes on its platform, the disappearance of this source code from GitHub after the government action raised the specter of government action chilling the publication of this code."
The EFF is right to be concerned, but there doesn't appear to be any evidence that the takedown was anything other than a decision by Microsoft. This is reinforced by the fact that Prof. Matthew Green's fork of Tornado Cash has not been removed.
The headline of Olga Kharif's Key Player In Ethereum Infrastructure Infura Rejects Centralization Claim is wrong. Infura actually admits that it has effectively centralized Ethereum, and promises probably ineffectual measures to fix the problem sometime in the future:
"At times, more than 50% of transactions on the Ethereum network ran through Infura, according to Eleazar Galano, the company’s co-founder. So its plan to offer a decentralized version of the service -- likely to launch in the first half of 2023 -- could have major implications for who holds power on Ethereum."
Note that a "decentralized version of the service" is necessarily going to be slower and more expensive than the current centralized service, because it will have extra overhead.
Molly White reports that:
"The Nostr Assets bitcoin platform has had to ask people to stop depositing into their platform because it's all clogged up. The project uses the bitcoin Lightning Network, which itself is an attempt to overcome the slowness and high cost of the bitcoin network. However, it too has limited capacity, and Nostr Assets has announced that the "inbound capacity of lightning channels" was depleted."
No comment. See this 2020 paper:
"The costs of running the attack are extremely low. We evaluate these costs in the Lightning Network where we show that using less than half a bitcoin, the attacker can indefinitely lock up channels holding the majority of the funds currently assigned to all channels."
Post a Comment