 |
| Source |
It was about 4 in the afternoon on Wednesday on the East Coast when chaos struck online. Dozens of the biggest names in America — including Joseph R. Biden Jr., Barack Obama, Kanye West, Bill Gates and Elon Musk — posted similar messages on Twitter: Send Bitcoin and the famous people would send back double your money.Two days later Nathaniel Popper and Kate Conger's Hackers Tell the Story of the Twitter Attack From the Inside was based on interviews with some of the perpetrators:
Mr. O'Connor said other hackers had informed him that Kirk got access to the Twitter credentials when he found a way into Twitter’s internal Slack messaging channel and saw them posted there, along with a service that gave him access to the company’s servers. People investigating the case said that was consistent with what they had learned so far. A Twitter spokesman declined to comment, citing the active investigation.Below the fold, some commentary on this and other stories of the fiasco.
First, this isn't the first illustration that Twitter's security is based on the long outdated idea that anyone inside the firewall is trusted:
In 2017, on his last day of work, an employee shut down President Donald Trump’s account. In 2019, two people were charged with spying for the Saudi government while they were Twitter employees.And even earlier:
In 2013, an attacker took over the Associated Press Twitter account and posted that the White House had been bombed and Barack Obama injured and Wall Street flash-crashed.Seriously, WTF Twitter? Despite these warnings, it appears credentials giving almost unrestricted access to Twitter's systems were posted on their Slack system! This is the enterprise version of the user's password on a PostIt stuck to their monitor.
Any company that took security seriously would have implemented token-based two-factor authentication for access to all internal systems, as for example Google has done since 2017:
Google has not had any of its 85,000+ employees successfully phished on their work-related accounts since early 2017, when it began requiring all employees to use physical Security Keys in place of passwords and one-time codes, the company told KrebsOnSecurity.So even long before 2017 no-one could have gained access to Google's systems by phishing an employee. Twitter's board should fire Jack Dorsey for the fact that, after at least seven years of insider attacks, their systems were still vulnerable.
...
A Google spokesperson said Security Keys now form the basis of all account access at Google.
“We have had no reported or confirmed account takeovers since implementing security keys at Google,” the spokesperson said. “Users might be asked to authenticate using their security key for many different apps/reasons. It all depends on the sensitivity of the app and the risk of the user at that point in time.”
...
prior to 2017 Google employees also relied on one-time codes generated by a mobile app — Google Authenticator.
Bruce Schneier's The Twitter Hacks Have to Stop points out the bigger picture (my emphasis):
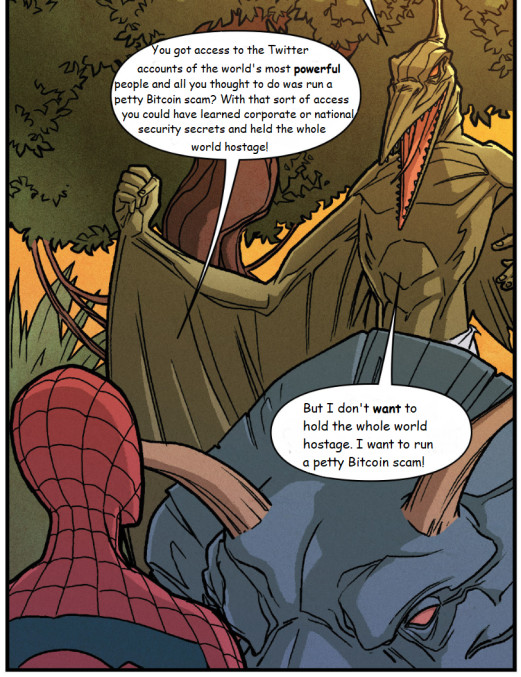
The hacker used that access to send tweets from a variety of popular and trusted accounts, including those of Joe Biden, Bill Gates, and Elon Musk, as part of a mundane scam—stealing bitcoin—but it’s easy to envision more nefarious scenarios. Imagine a government using this sort of attack against another government, coordinating a series of fake tweets from hundreds of politicians and other public figures the day before a major election, to affect the outcome. Or to escalate an international dispute. Done well, it would be devastating.Schneier has two suggestions for action:
Whether the hackers had access to Twitter direct messages is not known. These DMs are not end-to-end encrypted, meaning that they are unencrypted inside Twitter’s network and could have been available to the hackers. Those messages—between world leaders, industry CEOs, reporters and their sources, heath [sic] organizations—are much more valuable than bitcoin. (If I were a national-intelligence agency, I might even use a bitcoin scam to mask my real intelligence-gathering purpose.) Back in 2018, Twitter said it was exploring encrypting those messages, but it hasn’t yet.
Internet communications platforms—such as Facebook, Twitter, and YouTube—are crucial in today’s society. They’re how we communicate with one another. They’re how our elected leaders communicate with us. They are essential infrastructure. Yet they are run by for-profit companies with little government oversight. This is simply no longer sustainable. Twitter and companies like it are essential to our national dialogue, to our economy, and to our democracy. We need to start treating them that way, and that means both requiring them to do a better job on security and breaking them up.Treating these companies as utilities and regulating them:
...
There are many security technologies companies like Twitter can implement to better protect themselves and their users; that’s not the issue. The problem is economic, and fixing it requires doing two things. One is regulating these companies, and requiring them to spend more money on security. The second is reducing their monopoly power.
The security regulations for banks are complex and detailed. If a low-level banking employee were caught messing around with people’s accounts, or if she mistakenly gave her log-in credentials to someone else, the bank would be severely fined. Depending on the details of the incident, senior banking executives could be held personally liable. The threat of these actions helps keep our money safe. Yes, it costs banks money; sometimes it severely cuts into their profits. But the banks have no choice.Using anti-trust enforcement:
The opposite is true for these tech giants. They get to decide what level of security you have on your accounts, and you have no say in the matter. If you are offered security and privacy options, it’s because they decided you can have them. There is no regulation. There is no accountability. There isn’t even any transparency. Do you know how secure your data is on Facebook, or in Apple’s iCloud, or anywhere? You don’t. No one except those companies do. Yet they’re crucial to the country’s national security. And they’re the rare consumer product or service allowed to operate without significant government oversight.
In addition to security measures, the other solution is to break up the tech monopolies. Companies like Facebook and Twitter have so much power because they are so large, and they face no real competition. This is a national-security risk as well as a personal-security risk. Were there 100 different Twitter-like companies, and enough compatibility so that all their feeds could merge into one interface, this attack wouldn’t have been such a big deal. More important, the risk of a similar but more politically targeted attack wouldn’t be so great. If there were competition, different platforms would offer different security options, as well as different posting rules, different authentication guidelines—different everything. Competition is how our economy works; it’s how we spur innovation. Monopolies have more power to do what they want in the quest for profits, even if it harms people along the way.
 |
| Source |
David Gerard's Twitter Got Lucky With the Great Bitcoin Heist (backstory here) looks at the cryptocurrency scam that the attackers ran:
All scams are old scams. The words “double your money” are perfectly designed to catch the eye of the gullible. These days, money moves at the speed of light. So the scams work as a widely spammed numbers game: If you come up with something that looks like an obvious scam, only the gullible respond.He also points out how lax Twitter has been at preventing scams:
Bitcoin was designed to be unstoppable electronic money, with no central controller. Nobody can stop you sending your bitcoins anywhere you want to, and transactions are irreversible by design—a feature that was argued to be one of Bitcoin’s advantages.
Bitcoin doublers have been around since bitcoins could first be exchanged for real money—and earlier versions of the doubling scam ran in online games, such as “ISK doublers” in Eve Online or “coin doublers” in RuneScape. Send in a small amount of bitcoins, and you’ll get double the coins back! Send a larger amount straight after, and you won’t.
No reason is given for why anyone would just double your money. You’d think people would catch on, but, years later, this scam keeps popping up and finding suckers.
After the scam runs for the first time, there’s often a second layer: The doubler never sends back coins. But the doubling site is publicized with a “warning” about the scam. Others think: “If I only send coins once, the site will never see me as a repeat user!” They send in a small amount of coins—and never get anything back, even once. Like all the best scams, it’s a scam that relies on the sucker thinking they’re the scammer.
The social media platform has let coin doubling scams for Ethereum, another prominent cryptocurrency, run rampant for the past few years. Tweet with an avatar and a display name imitating some famous person, saying you’ll double people’s ether. Add some replies thanking the famous person for the money. These could pull in up to $5,000 a day in ether. Ethereum’s creator, Vitalik Buterin, eventually added “Not giving away ETH” to his Twitter display name for a time.Overall, this is a depressing situation. There is the potential for a truly catastrophic Twitter hack. Twitter has demonstrated that they don't care enough about security to implement basic precautions. There's no incentive for them to change this attitude, because neither regulation nor anti-trust willbe applied to them. All we can do is to wait for the explosion that is bound to come.
Elon Musk has long been another favorite target—to the point where Twitter would stop users from changing their display name to “Elon Musk.” One 2018 Musk scam pulled in $180,000 in bitcoins.
8 comments:
As usual, the compromise was worse than at first appeared. Dan Goodin's Hackers obtained Twitter DMs for 36 high-profile account holders has more details:
"Hackers accessed direct messages for 36 high-profile account holders in last week’s epic compromise of Twitter, with one of the affected users being an elected official from the Netherlands, the social media company said late Wednesday. The company also said the intruders were able to view email addresses, phone numbers, and other personal information for all 130 hijacked accounts."
YouTube is also rife with cryptocurrency scams, as Timothy B. Lee reports in Woz sues YouTube over “bitcoin giveaway” scam videos using his name:
"Apple co-founder Steve Wozniak has sued YouTube over the proliferation of "bitcoin giveaway" scam videos on the YouTube platform. The videos falsely use the names of Wozniak and other celebrities—including Elon Musk, Bill Gates, and Ethereum founder Vitalik Buterin—to give the scams legitimacy.
Scammers hijack popular YouTube accounts and change their names so that they appear to be the official accounts of celebrities like Wozniak or companies like Apple. They then broadcast a "live" video showing old footage of the celebrity discussing cryptocurrency or related topics. Alongside the footage is text claiming that if someone sends bitcoin to a particular address, the celebrity would send back double the amount.
Along with Wozniak, the plaintiffs include more than a dozen individuals who were taken in by the scam, losing bitcoins worth anywhere from a few dollars to more than $40,000. In total, cryptocurrency scams like this have cost victims millions of dollars."
However:
"The plaintiffs argue that YouTube did more than passively host the videos. YouTube's recommendation algorithms promoted the videos to cryptocurrency enthusiasts and sold ads against the videos—directly profiting from the scams. But that could also be a hard sell; courts have repeatedly held that sites enjoy Section 230 protections even when they deliberately promote problematic third-party content."
The title says it all. More than 1,000 people at Twitter had ability to aid hack of accounts by Joseph Menn, Katie Paul, and Raphael Satter reports that:
"More than a thousand Twitter employees and contractors as of earlier this year had access to internal tools that could change user account settings and hand control to others, two former employees said, making it hard to defend against the hacking that occurred last week.
...
The former employees familiar with Twitter security practices said that too many people could have done the same thing, more than 1,000 as of earlier in 2020, including some at contractors like Cognizant."
Not to mention everyone who could read their internal Slack channel. But not to worry:
"The company was looking for a new security head, working to better secure its systems and training employees on resisting tricks from outsiders, Twitter said."
So that's OK, then.
Ian Bogost's So Much for the Decentralized Internet is a pretty good overview:
"The hack makes Twitter look incompetent, and at a bad time; its advertising revenues are falling, and the company is scrambling to respond. It also underscores the impoverished cybersecurity at tech firms, which provide some employees with nearly limitless control over user accounts and data—as many as 1,000 Twitter employees reportedly had access to the internal tools that were compromised. But the stakes are higher, too. Though much smaller than Facebook in terms of its sheer number of users, Twitter is where real-time information gets published online, especially on news and politics, from a small number of power users. That makes the service’s vulnerability particularly worrisome; it has become an infrastructure for live information. The information itself had already become weaponized; now it’s clear how easily the actual accounts publishing that information can be compromised too. That’s a terrifying prospect, especially in the lead-up to the November U.S. presidential election featuring an incumbent who uses Twitter obsessively, and dangerously."
A post on Twiiter's blog reports that:
"The social engineering that occurred on July 15, 2020, targeted a small number of employees through a phone spear phishing attack. A successful attack required the attackers to obtain access to both our internal network as well as specific employee credentials that granted them access to our internal support tools. Not all of the employees that were initially targeted had permissions to use account management tools, but the attackers used their credentials to access our internal systems and gain information about our processes. This knowledge then enabled them to target additional employees who did have access to our account support tools."
The bad guys only had to find 1 of the around 1K employees with the necessary access. CNN comments:
"While the scope of the incident was massive in its own right, it could merely be the tip of a very large iceberg with vast security implications. Cybersecurity experts and policymakers now worry that the bitcoin scam may mask a much more troubling data breach involving the personal communications of the world's most powerful people."
This press release, HILLSBOROUGH STATE ATTORNEY’S OFFICE TAPPED TO PROSECUTE WORLDWIDE “BIT-CON” HACK OF PROMINENT TWITTER USERS, reports that:
"Hillsborough State Attorney Andrew Warren has filed 30 felony charges against a Tampa resident for scamming people across America, perpetrating the “Bit-Con” hack of prominent Twitter accounts including Bill Gates, Barack Obama, and Elon Musk on July 15, 2020.
The Federal Bureau of Investigation and the U.S. Department of Justice conducted a complex nationwide investigation, locating and apprehending the suspect in Hillsborough County.
...
The investigation revealed Graham Ivan Clark, 17, was the mastermind of the recent hack of Twitter. He was arrested in Tampa early on July 31. Clark’s scheme to defraud stole the identities of prominent people, posted messages in their names directing victims to send Bitcoin to accounts associated with Clark, and reaped more than $100,000 in Bitcoin in just one day. As a cryptocurrency, Bitcoin is difficult to track and recover if stolen in a scam."
Nicholas Thompson and Brian barrett's How Twitter Survived Its Biggest Hack—and Plans to Stop the Next One details the moat-based security that led to Twitter's July 15 catastrophe:
"Alex Stamos, the former chief security officer of Facebook, says he’s surprised that a phishing scheme of customer service reps could lead to a total shutdown. Based on his understanding of the public record, it would have been much better for Twitter to just analyze its logs and shut down the accounts causing all the trouble. “These are the kinds of steps you take if you have the Ministry of State Security inside your Active Directory,” he says, referring to the home of China’s elite state-sponsored hackers.
Another former senior Twitter employee says roughly the same thing: “There was a systems-level failure. The whole thing should not have happened. The issue isn’t that someone got phished; it’s that once they got phished, the company should have had the right systems in place.”"
I agree, but it isn't the case that someone getting phished is OK. Twitter should have enforced security tokens, as Google has done for three years. Twitter was incompetent both ways, but they are now shutting the stable door:
"But one of the first things Twitter realized in the immediate aftermath was that too many people had too much access to too many things. “It’s more about how much trust you’re putting in each individual, and in how many people do you have broad-based trust,” Agrawal says. “The amount of access, the amount of trust granted to individuals with access to these tools, is substantially lower today.”
One of the biggest changes the company has implemented is to require all employees to use physical two-factor-authentication. Twitter had already started distributing physical security keys to its employees prior to the hack, but stepped up the program’s rollout. Within a few weeks, everyone at Twitter, including contractors, will have a security key and be required to use it."
The article was published less than six weeks before the election. Lets hope "a few weeks" is less than six.
Twitter stopped working about 2:30PDT Mark Frauenfelder writes:
"[UPDATE 4:30pm PT: Sadly, Twitter is functional again"
Post a Comment